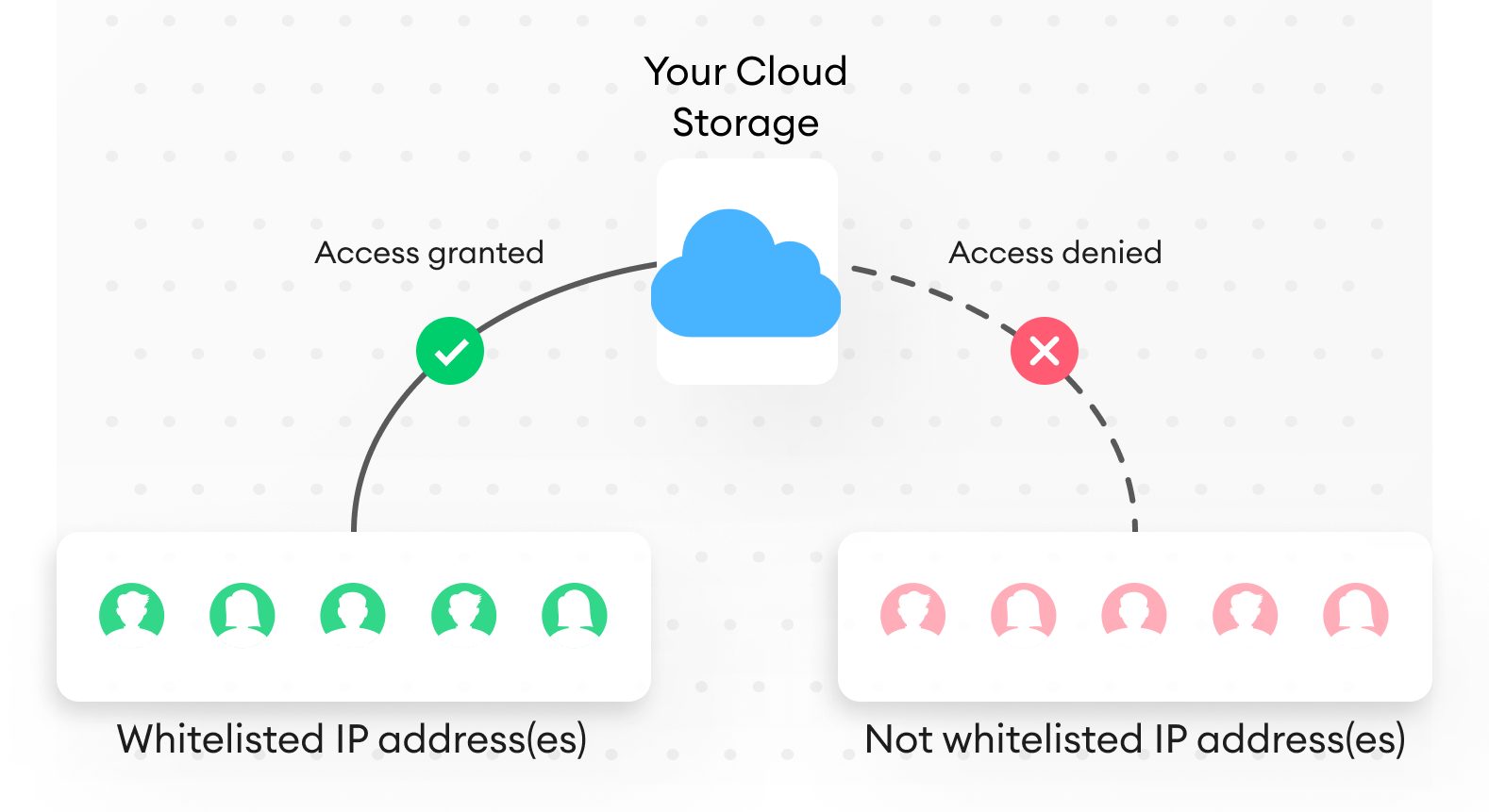
IP whitelisting
IP whitelisting is a way of giving access to your data to specific, trusted, and pre-approved IP addresses. This increases the security of your data and ensures safe remote access.
Here's the list of SuperAnnotate IPs you may need to whitelist when using integrations (for AWS and Azure, you can read more about the process below):
54.204.115.30
100.24.156.84
54.83.51.100
34.239.194.194
Here's the list of SuperAnnotate URLs you may need to whitelist in case of any access difficulties:
3d.superannotate.com
api.superannotate.com
app.superannotate.com
assets.superannotate.com
assets-api.superannotate.com
assets-provider.superannotate.com
auth.superannotate.com
blog.superannotate.com
custom-llm.superannotate.com
custom-storage.superannotate.com
datasets.superannotate.com
doc.superannotate.com
document.superannotate.com
editor.superannotate.com
explore.superannotate.com
explore.api.superannotate.com
explore-service.superannotate.com
files.superannotate.com
hooks.superannotate.com
item.superannotate.com
llm.superannotate.com
mcp.superannotate.com
ml-api.superannotate.com
ms.superannotate.com
pixel.superannotate.com
public.superannotate.com
public-static-files.superannotate.com
status.superannotate.com
telemetry.superannotate.com
telemetry-scoring.superannotate.com
telemetry-search-service.superannotate.com
vector.superannotate.com
vectort.superannotate.com
video.superannotate.com
work-management-api.superannotate.com
work-metrics-api.superannotate.com
zimmer.superannotate.com
AWS
How can I restrict access to my S3 bucket by IP address?
To give access to your S3 bucket to a specific IP address, you need to create a policy for your S3 bucket or edit it if you already have one.
Policy example
The following policy gives access to the following IP address 54.240.143.0/24. With this IP address, you can access the buckets stated in Resource. What you need to do is replace the values in Resource and IpAddress with your own values and create or edit the policy of your bucket.
{
"Version": "2012-10-17",
"Id": "S3Allowlisting",
"Statement": [
{
"Sid": "IPAllow",
"Effect": "Allow",
"Principal": "*",
"Action": "s3:*",
"Resource": [
"arn:aws:s3:::DOC-EXAMPLE-BUCKET",
"arn:aws:s3:::DOC-EXAMPLE-BUCKET/*"
],
"Condition": {
"IpAddress": {
"aws:SourceIp": ["54.240.143.0/24", "53.456.987.0/87"]
}
}
}
]
}Statement key
Since the statement key is an array, you can add multiple statements for different files and folders.
Condition block
The condition block consists of the IpAddress condition and the aws:SourceIp condition key.
The aws:SourceIp condition key is an AWS-wide condition key. Learn more about condition keys.
The values of aws:SourceIp IPv4 use the standard CIDR notation. For more information, check out the IAM JSON policy elements reference.
How can I create or edit the policy of my S3 bucket?
To create or edit as S3 bucket’s policy:
- Go to your Amazon S3 console.
- Go to the bucket where you want to create a policy.
- Select the Permissions tab.
- Click Edit next to Bucket policy.
- Add or edit the policy as explained here.
- Click Save changes.
Azure
Azure offers 2 options to restrict access to Azure resources from the given range of IP addresses:
- Put a firewall with the list of IP addresses on the Azure storage account.
- Generate an IP-restricted SAS token on an Azure account/container/blob.
Method 1
This method allows you to make the container’s blobs accessible only from the given range of IP addresses.
- Go to your storage account.
- Under Data storage, select Containers.
- Select the container.
- Click Change access level.
- Under Public access level, choose Blob (anonymous read access for blobs only).
- Click OK.
- Under Security + Networking, select Networking.
- Under Firewall, add the IP address or the IP addresses and ranges that you want to whitelist.
Click here for more details.
To add these Blob URLs to SuperAnnotate, use the attach_items function.
Method 2
This method allows you to generate a shared access token with IP restrictions and use it in the signed URL of the given resource. You can use this method for storage accounts, containers, and blobs.
The following steps describe the setup of the container’s SAS token. You can use this method to also generate a SAS token for storage accounts and blobs.
- Go to your container.
- Choose Shared access tokens under Settings.
- Under Allowed IP addresses, define the IP address or the IP range that are allowed to access the container.
- Click Generate SAS token and URL.
- Save the generated SAS token.
Click here for more details.
With this method, the container blobs will be accessible from the given range of IP addresses via signed URLs.
To attach these URLs to SuperAnnotate, create a CSV file that contains these URLs and use it in the attach_items SDK function.
IP whitelisting recipe
from azure.storage.blob import BlobServiceClient
from azure.storage.blob import ContainerSasPermissions, generate_container_sas
from datetime import datetime, timedelta
from superannotate import SAClient
import os
azure_connection_string = "<your_connection_string>"
azure_container_name = "<your_container_name>"
authorized_ip = "<authorized_ip_or_ip_range>"
blob_service_client = BlobServiceClient.from_connection_string(azure_connection_string)
container_client = blob_service_client.get_container_client(azure_container_name)
#Generate a container SAS token with an expiry date and IP whitelisting.
sas_token = generate_container_sas(
account_name = container_client.account_name,
container_name = container_client.container_name,
account_key=container_client.credential.account_key,
permission=ContainerSasPermissions(read=True),
expiry=datetime.utcnow() + timedelta(days=30),
start=datetime.utcnow() - timedelta(minutes=1),
ip = authorized_ip)
#Generate signed URLs on container blobs with the generated container SAS token.
attachments = []
for blob in container_client.list_blobs():
signed_url = f"{blob_service_client.url}{container_client.container_name}/{blob.name}?{sas_token}"
attachments.append({'name': blob.name, 'url': signed_url})
#Create a SuperAnnotate project and attach the generated signed URLs to it.
sdk_token = "<your_sdk_token>"
sa_client = SAClient(token=sdk_token)
sa_client.create_project(azure_container_name, "---", "Vector")
sa_client.attach_items(azure_container_name, attachments)Updated 4 days ago